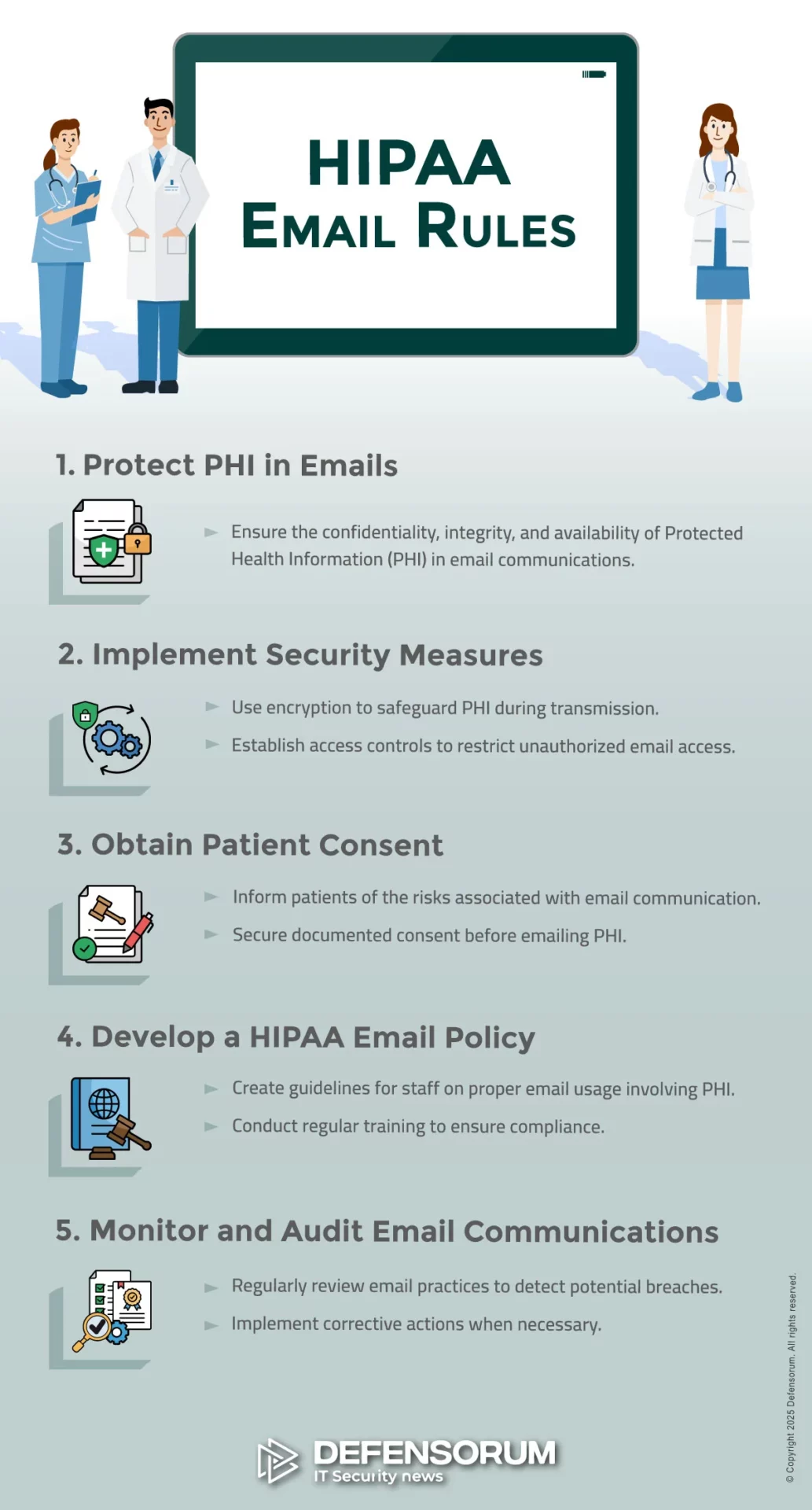
The HIPAA email rules are that email can only be used to send, receive, or store Protected Health Information (PHI) if the reason for PHI being disclosed is consistent with the Privacy Rule, and if safeguards are in place to protect the confidentiality, integrity, and availability of PHI in transit and at rest.
One of the challenges of HIPAA email compliance is that the HIPAA email rules can apply to different organizations in different ways. How PHI is communicated, the type of organization, and patients’ preferences can all have an impact on HIPAA email compliance – notwithstanding that some states have “affirmative opt-in” email regulations that preempt HIPAA.
To further complicate HIPAA email compliance, standards relevant to sending PHI via email can be found throughout the HIPAA Administrative Simplification Regulations. The areas of the HIPAA Regulations with the most significance to the HIPAA email rules are the General Administrative Requirements, the HIPAA Privacy Rule, and the HIPAA Security Rule.
Who Do The HIPAA Email Rules Apply To?
It is important to note that the HIPAA Administrative Simplification Regulations protect the privacy and security of PHI. If PHI is not disclosed in email communications nor stored in an email folder, the HIPAA email rules do not apply – although state consumer privacy laws may apply to individually identifiable non-health information.
If PHI is disclosed in email communications, the HIPAA email rules apply to health plans, health care clearinghouses, and healthcare providers that qualify as HIPAA covered entities. The HIPAA email rules also apply to business associates who provide a service for or on behalf of a covered entity, if the service involves disclosures of PHI via email.
The General Administrative Requirements (§160.103) includes definitions of “covered entities”, “business associates”, and “protected health information”. Definitions of “uses” and “disclosures” are also included. Organizations that are unsure about whether the HIPAA email rules apply to them should seek professional compliance advice.
Privacy Rule HIPAA Email Compliance
The HIPAA Privacy Rule governs uses and disclosures of PHI, the conditions that must be in place before PHI is shared with a business associate, and the rights patients have over how their PHI is used or disclosed – including the right to receive PHI by email, even when a covered entity’s email system does not support HIPAA compliance.
Required and Permitted Uses and Disclosures of PHI
There are only two circumstances in which a disclosure of PHI is required – when the subject of the PHI (i.e., a patient) requests a copy of their PHI and when officials from HHS’ Office for Civil Rights request PHI to conduct a compliance investigation or audit. In both these circumstances, the minimum necessary standard does not apply.
A covered entity can use or disclose PHI for multiple permitted purposes including treatment, payment, and healthcare operations, and when sending PHI by email is allowed by §164.512. Sending patient information by email is also permitted when a patient or their personal representative has signed a valid HIPAA authorization.
PHI and Business Associates
PHI can be disclosed to business associates in many different circumstances. For example, a billing company might process health insurance claims on behalf of a hospital, a medical answering service might handle incoming calls on behalf of a physician, or a dentist might use a cloud based productivity service such as Google Workspace.
In all circumstances in which PHI is disclosed to a business associate – including when a business associate has “no view access” to PHI – covered entities and business associates must enter into a Business Associate Agreement that complies with the requirements of §164.504(e). The failure to enter into an Agreement is a HIPAA violation.
Patients and HIPAA Email Compliance
Patients’ preferences can have an impact on HIPAA email compliance inasmuch as patients can request copies of their PHI via email, authorize a disclosure of PHI via email, and request confidential communications via email (§164.522(b)). In all circumstances a covered entity must accommodate the requests when they are “reasonable”.
This means that, even when a covered entity’s email system does not support HIPAA compliance (i.e., because it does not have the safeguards required by the Security Rule), covered entities are required to comply with patients’ preferences. When this occurs, patients should be warned of the risks and the warning should be documented.
HIPAA Email Security Rule Compliance
The introduction to the HIPAA email Security Rule standards further complicate HIPAA email compliance by allowing a “flexibility of approach”. This gives covered entities and business associates the opportunity to take into account factors such as cost and complexity when determining how they will comply with the Security Rule’s HIPAA email requirements.
Administrative HIPAA Email Security Requirements
The Administrative HIPAA email security requirements include standards relating to risk assessments, risk management planning, and workforce security awareness training. The Administrative HIPAA email security requirements also include contingency planning and further requirements for Business Associate Agreements.
With regards to Business Associate Agreements, these have to be in place with each HIPAA compliant email service used by the organization, including email encryption services if used as an addition to an existing email service – for example, Microsoft 365 and Paubox. An exception to this rule exists if all email services are managed by an MSP.
Physical HIPAA Email Security Requirements
Many of the Physical email security requirements only apply if a covered entity or business associate has an on-premises email server. For example, the location of the mail server determines who is responsible for controlling physical access to the server, maintenance of the server, and ensuring the availability of PHI during an outage.
However, the physical HIPAA email security requirements also apply to workstations and mobile devices that send, receive, or store PHI. As the Physical HIPAA email security requirements were adopted before mobile devices had the capabilities they have now, covered entities and business associates should factor this into their risk assessments.
Technical HIPAA Email Security Requirements
The risk assessments will help determine how covered entities and business associates deal with the mostly “addressable” standards and implementation specifications of the Technical HIPAA email security requirements. For example, can manual audit logs be used to comply with the audit control requirements, or is it necessary to implement an automated system?
Some requirements are easier to comply with now than when the Security Rule was originally published. For example, most devices are now configured with automatic log-off capabilities by default. To comply with this implementation specification, covered entities only need to ensure the capabilities are activated and cannot be overridden.
The HIPAA Email Encryption Requirements
Although an addressable implementation specification of the Technical HIPAA email encryption requirements, the only way in which it would be possible to avoid implementing the HIPAA email encryption requirements is if all email communications containing PHI are internal and protected by a firewall (see definition of “disclosure” in §160.103).
The HIPAA Encrypted Email Requirements
Although HHS’ Office for Civil Rights has acknowledged the HIPAA encrypted email requirements are not mandatory, the agency published guidance in 2013 on the types of encryption that would be necessary to comply with the implementation specifications for PHI in transit and at rest in the Security Rule’s Technical Safeguards.
For PHI in transit, the guidance recommends encryption processes that align with NIST SP 800-52 (TLS 1.2 or higher) or “others which are FIPS 140-2 validated” (for example, OpenPGP and S/MIME). For PHI at rest, the guidance recommends covered entities and business associates apply the standards recommended in NIST SP 800-111 (AES-128 or higher).
Compliance with the HIPAA Encrypted Email Requirements
The responsibility for complying with the HIPAA encrypted email requirements for PHI in transit is situation specific. For example, if a covered entity hosts an email server on premises, but the email service or an email encryption service is provided by a business associate (i.e., Exchange Server 2019), the business associate is responsible for compliance
Similarly, the responsibility for compliance with the HIPAA encrypted email requirements for PHI at rest depends on whether the organization’s email server is hosted on-premises, hosted in the cloud by a HIPAA compliant email service provider, or provided by a Managed Service Provider. In the first scenario, the organization is responsible for encrypting PHI at rest.
Is Encrypted Email HIPAA Compliant?
Encrypted email that meets the standards of the guidance published by HHS’ Office for Civil Rights is HIPAA compliant, but encryption alone does not guarantee compliance with the HIPAA email rules. In order to comply with the HIPAA email rules, covered entities and business associates have to comply with all applicable Privacy and Security Rule standards.
This is because encryption does not prevent unauthorized access to PHI when a member of the workforce interacts with a phishing email, sends an email containing PHI to the wrong recipient, forgets to use the Blind Carbon Copy (BCC) function when sending emails containing PHI to multiple recipients, or sends PHI to a personal account.
Does HIPAA Allow Email Breach Notifications?
HIPAA allows email breach notifications only when an individual has previously consented to receive notifications by email and consent has not been withdrawn (§164.404). The reason for this is that although breach notifications do not contain PHI, an email from certain types of healthcare provider could be embarrassing for the recipient.
Although it seems logical that individuals would want to be notified of a data breach as quickly as possible to protect themselves from fraud or theft, individuals must be notified of a data breach by first class mail even when an individual has previously consented (or requested) to receive – for example – appointment reminders by email.
State Regulations and HIPAA Compliance for Email
Most states have consumer privacy and/or breach notification regulations. Many state regulations exempt HIPAA covered entities and/or business associates and/or PHI. However, some states may exempt (for example) covered entities and PHI, but not business associates providing a service to the covered entity using the same PHI.
It is important for organizations to understand which state regulations apply to what type(s) of data. For example, some states require consumers to affirmatively opt in before their email address can be recorded by an organization. In theory, an organization could be in compliance with HIPAA, but in violation of a state regulation.
Training Workforces on the HIPAA Requirements for Email
Because all members of the workforce are likely to use email in their work or private lives, it is important that all members of the workforce receive HIPAA training on the HIPAA requirements for email in addition to the mandatory security awareness training. This effectively means providing Privacy Rule training at the same time as Security Rule training.
It should be noted that §164.530(e) of the Privacy Rule requires covered entities to impose sanctions on members of the workforce that fail to comply with the HIPAA Privacy Rule. If members of the workforce are not trained on the HIPAA Privacy Rule, the covered entity is responsible for any HIPAA violation attributable to a lack of training.
HIPAA Email Rules Compliance Checklist
This checklist has been compiled to summarize what has been discussed above. The completion of the checklist does not guarantee compliance with the HIPAA email rules and organizations in need of further information or concerned about their compliance obligations should seek professional compliance advice.
- Does Your organization qualify as a HIPAA covered entity or business associate? If not, the HIPAA email rules do not apply.
- Does your organization send emails containing PHI to recipients outside your organization? If not, the HIPAA email rules do not apply.
- Do members of the workforce with authorized access to PHI understand when it is required or permitted to send PHI in an email?
- Do members of the workforce with authorized access to PHI understand when the minimum necessary standard applies?
- Has the organization entered into Business Associate Agreements with all third parties to whom PHI is disclosed by email?
- If applicable, has the organization entered into Business Associate Agreements with email service and encryption service providers?
- Has the organization conducted a risk assessment to identify threats and vulnerabilities to the security of PHI in emails?
- Has the organization implemented policies and procedures to mitigate threats and vulnerabilities to the security of PHI in emails?
- Has the organization developed and adopted policies and procedures to comply with all applicable Physical Safeguards?
- Has the organization complied with all applicable Technical Safeguards and documented the reasons for non-compliance with addressable Safeguards?
- Has the organization complied with the HIPAA email encryption standards to the specifications recommended by HHS’ Office for Civil Rights?
- Has the organization developed procedures to identify when an individual requests confidential communications or breach notifications by email?
- Has the organization integrated state regulations into its HIPAA compliant email policy? Have all workforce members received training on the policy?
Image Credit: ©Defensorum / Banana Images; Stock.adobe.com